《iOS應用安全攻防》掃描版[PDF] 簡介: 中文名 : iOS應用安全攻防 作者 : Jonatban Zdziarski 圖書分類 : 軟件 資源格式 : PDF 版本 : 掃描版 出版社 : 東南大學出版社 書號 : 0787020002207 發行時間 : 2012年 地區 : 大陸 語言 : 英文 簡介 : 內容介紹: 《iOS應用安全攻防(影印版)(英文)》絕對急你所需——你所在公司的iOS應
"《iOS應用安全攻防》掃描版[PDF]"介紹
中文名: iOS應用安全攻防
作者: Jonatban Zdziarski
圖書分類: 軟件
資源格式: PDF
版本: 掃描版
出版社: 東南大學出版社
書號: 0787020002207
發行時間: 2012年
地區: 大陸
語言: 英文
簡介:
內容介紹:
《iOS應用安全攻防(影印版)(英文)》絕對急你所需——你所在公司的iOS應用被攻擊的可能性很大。這是因為惡意攻擊者現在使用一系列工具采用大多數程序員想象不到的方式進行反向工程、跟蹤和操縱應用。這本《iOS應用安全攻防(影印版)(英文)》講解了幾種iOS的攻擊手段,以及黑客們常用的工具和技術。你會從中學到保護你的應用的最佳方式,並且意識到像你的對手那樣去理解和制定策略是多麼重要。
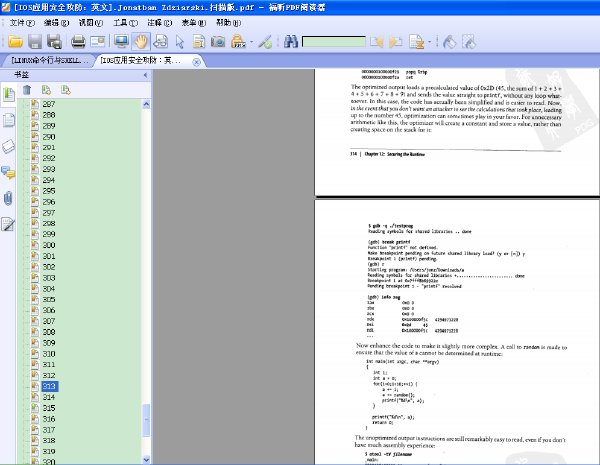
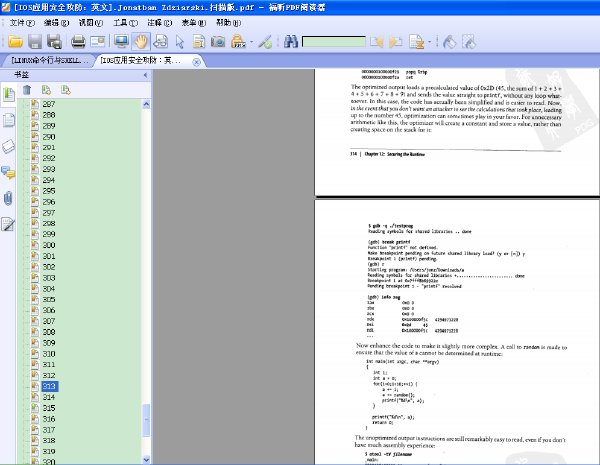
內容截圖:
目錄:
1. Everything You Know Is Wrong
The Myth of a Monoculture
The iOS Security Model
Components of the iOS Security Model
Storing the Key with the Lock
Passcodes Equate to Weak Security
Foreic Data Trumps Encryption
External Data Is at Risk, Too
Hijacking Traffic
Data Can Be Stolen...Quickly
Trust No One, Not Even Your Application
Physical Access Is Optional
Summary
Part Ⅰ. Hacking
2. The Basics of Compromising iOS
Why It's Important to Learn How to Break Into a Device
Jailbreaking Explained
Developer Tools
End User Jailbreaks
Jailbreaking an iPhone
DFU Mode
Tethered Veus Untethered
Compromising Devices and Injecting Code
Building Custom Code
Analyzing Your Binary
Testing Your Binary
Daemon!zing Code
Deploying Malicious Code with a Tar Archive
Deploying Malicious Code with a RAM Disk
Exercises
Summary
3. Stealing the Filesystem
Full Disk Encryption
Solid State NAND
Disk Encryption
Where lOS Disk Encryption Has Failed You
Copying the Live Filesystem
The DataTheft Payload
Customizing launchd
Preparing the RAM disk
Imaging the Filesystem
Copying the Raw Filesystem
The RawTheft Payload
Customizing launchd
Preparing the RAM disk
Imaging the Filesystem
Exercises
The Role of Social Engineering
Disabled Device Decoy
Deactivated Device Decoy
Malware Enabled Decoy
Password Engineering Application
Summary
4. Foreic Trace and Data Leakage
Extracting Image Geotags
Coolidated GPS Cache
SQLite Databases
Connecting to a Database
SQLite Builtin Commands
Issuing SQL Queries
Important Database Files
Address Book Contacts
Address Book Images
Google Maps Data
Calendar Events
Call History
Email Database
Notes
Photo Metadata
SMS Messages
Safari Bookmarks
SMS Spotlight Cache
Safari Web Caches
Web Application Cache
WebKit Storage
Voicemail
Revee Engineering Remnant Database Fields
SMS Drafts
Property Lists
Important Property List Files
Other Important Files
Summary
5. Defeating Encryption
Sogeti's Data Protection Tools
Italling Data Protection Tools
Building the Brute Forcer
Building Needed Python Libraries
Extracting Encryption Keys
The KeyTheft Payload
Customizing Launchd
Preparing the RAM disk
Preparing the Kernel
Executing the Brute Force
Decrypting the Keychain
Decrypting Raw Disk
Decrypting iTunes Backups
Defeating Encryption Through Spyware
The SpyTheft Payload
Daemonizing spyd
Customizing Launchd
Preparing the RAM disk
Executing the Payload
Exercises
Summary
6. Unobliterating Files
Scraping the HFS Journal
Carving Empty Space
Commonly Recovered Data
Application Screehots
Deleted Property Lists
Deleted Voicemail and Voice Recordings
Deleted Keyboard Cache
Photos and Other Peonal Information
Summary
7. Manipulating the Runtime
Analyzing Binaries
The MachO Format
Introduction to classdumpz
Symbol Tables
Encrypted Binaries
Calculating Offsets
Dumping Memory
Copy Decrypted Code Back to the File
Resetting the cryptid
Abusing the Runtime with Cycript
Italling Cycript
Using Cycript
Breaking Simple Locks
Replacing Methods
Trawling for Data
Logging Data
More Serious Implicatio
Exercises
SpringBoard Animatio
Call Tapping...Kind Of
Making Screen Shots
Summary
8. Abusingthe Runtime Library
Breaking ObjectiveC Down
Itance Variables
Methods
Method Cache
Disassembling and Debugging
Eavesdropping
The Underlying ObjectiveC Framework
Interfacing with ObjectiveC
Malicious Code Injection
The CodeTheft Payload
Injection Using a Debugger
Injection Using Dynamic Linker Attack
Full Device Infection
Summary
9. Hijacking Traffic
APN Hijacking
Payload Delivery
Removal
Simple Proxy Setup
Attacking SSL
SSLStrip
Paros proxy
Browser Warnings
Attacking ApplicationLevel SSL Validation
The SSLTheft Payload
Hijacking Foundation HTTP Classes
The POSTTheft Payload
Analyzing Data
Driftnet
Building
Running
Exercises
Summary
Part Ⅱ. Securing
10. Implementing Encryption
Password Strength
Beware Random Password Generato
Introduction to Common Crypto
Stateless Operatio
Stateful Encryption
Master Key Encryption
GeoEncryption
GeoEncryption with Passphrase
Split ServerSide Keys
Securing Memory
Wiping Memory
Public Key Cryptography
Exercises
11. Counter Foreics
Secure File Wiping
DOD 5220.22M Wiping
ObjectiveC
Wiping SQLite Records
Keyboard Cache
Randomizing PIN Digits
Application Screehots
12. Securing the Runtime
Tamper Respoe
Wipe User Data
Disable Network Access
Report Home
Enable Logging
False Contacts and Kill Switches
Process Trace Checking
Blocking Debugge
Runtime Class Integrity Checks
Validating Address Space
Inline Functio
Complicating Disassembly
Optimization Flags
Stripping
They're Fun! They Roll! funrollloops
Exercises
13. Jailbreak Detection
Sandbox Integrity Check
Filesystem Tests
Existence of Jailbreak Files
Size of/etc/fstab
Evidence of Symbolic Linking
Page Execution Check
14. Next Steps
Thinking Like an Attacker
Other Revee Engineering Tools
Security Veus Code Management
A Flexible Approach to Security
Other Great Books
作者: Jonatban Zdziarski
圖書分類: 軟件
資源格式: PDF
版本: 掃描版
出版社: 東南大學出版社
書號: 0787020002207
發行時間: 2012年
地區: 大陸
語言: 英文
簡介:
內容介紹:
《iOS應用安全攻防(影印版)(英文)》絕對急你所需——你所在公司的iOS應用被攻擊的可能性很大。這是因為惡意攻擊者現在使用一系列工具采用大多數程序員想象不到的方式進行反向工程、跟蹤和操縱應用。這本《iOS應用安全攻防(影印版)(英文)》講解了幾種iOS的攻擊手段,以及黑客們常用的工具和技術。你會從中學到保護你的應用的最佳方式,並且意識到像你的對手那樣去理解和制定策略是多麼重要。
內容截圖:
目錄:
1. Everything You Know Is Wrong
The Myth of a Monoculture
The iOS Security Model
Components of the iOS Security Model
Storing the Key with the Lock
Passcodes Equate to Weak Security
Foreic Data Trumps Encryption
External Data Is at Risk, Too
Hijacking Traffic
Data Can Be Stolen...Quickly
Trust No One, Not Even Your Application
Physical Access Is Optional
Summary
Part Ⅰ. Hacking
2. The Basics of Compromising iOS
Why It's Important to Learn How to Break Into a Device
Jailbreaking Explained
Developer Tools
End User Jailbreaks
Jailbreaking an iPhone
DFU Mode
Tethered Veus Untethered
Compromising Devices and Injecting Code
Building Custom Code
Analyzing Your Binary
Testing Your Binary
Daemon!zing Code
Deploying Malicious Code with a Tar Archive
Deploying Malicious Code with a RAM Disk
Exercises
Summary
3. Stealing the Filesystem
Full Disk Encryption
Solid State NAND
Disk Encryption
Where lOS Disk Encryption Has Failed You
Copying the Live Filesystem
The DataTheft Payload
Customizing launchd
Preparing the RAM disk
Imaging the Filesystem
Copying the Raw Filesystem
The RawTheft Payload
Customizing launchd
Preparing the RAM disk
Imaging the Filesystem
Exercises
The Role of Social Engineering
Disabled Device Decoy
Deactivated Device Decoy
Malware Enabled Decoy
Password Engineering Application
Summary
4. Foreic Trace and Data Leakage
Extracting Image Geotags
Coolidated GPS Cache
SQLite Databases
Connecting to a Database
SQLite Builtin Commands
Issuing SQL Queries
Important Database Files
Address Book Contacts
Address Book Images
Google Maps Data
Calendar Events
Call History
Email Database
Notes
Photo Metadata
SMS Messages
Safari Bookmarks
SMS Spotlight Cache
Safari Web Caches
Web Application Cache
WebKit Storage
Voicemail
Revee Engineering Remnant Database Fields
SMS Drafts
Property Lists
Important Property List Files
Other Important Files
Summary
5. Defeating Encryption
Sogeti's Data Protection Tools
Italling Data Protection Tools
Building the Brute Forcer
Building Needed Python Libraries
Extracting Encryption Keys
The KeyTheft Payload
Customizing Launchd
Preparing the RAM disk
Preparing the Kernel
Executing the Brute Force
Decrypting the Keychain
Decrypting Raw Disk
Decrypting iTunes Backups
Defeating Encryption Through Spyware
The SpyTheft Payload
Daemonizing spyd
Customizing Launchd
Preparing the RAM disk
Executing the Payload
Exercises
Summary
6. Unobliterating Files
Scraping the HFS Journal
Carving Empty Space
Commonly Recovered Data
Application Screehots
Deleted Property Lists
Deleted Voicemail and Voice Recordings
Deleted Keyboard Cache
Photos and Other Peonal Information
Summary
7. Manipulating the Runtime
Analyzing Binaries
The MachO Format
Introduction to classdumpz
Symbol Tables
Encrypted Binaries
Calculating Offsets
Dumping Memory
Copy Decrypted Code Back to the File
Resetting the cryptid
Abusing the Runtime with Cycript
Italling Cycript
Using Cycript
Breaking Simple Locks
Replacing Methods
Trawling for Data
Logging Data
More Serious Implicatio
Exercises
SpringBoard Animatio
Call Tapping...Kind Of
Making Screen Shots
Summary
8. Abusingthe Runtime Library
Breaking ObjectiveC Down
Itance Variables
Methods
Method Cache
Disassembling and Debugging
Eavesdropping
The Underlying ObjectiveC Framework
Interfacing with ObjectiveC
Malicious Code Injection
The CodeTheft Payload
Injection Using a Debugger
Injection Using Dynamic Linker Attack
Full Device Infection
Summary
9. Hijacking Traffic
APN Hijacking
Payload Delivery
Removal
Simple Proxy Setup
Attacking SSL
SSLStrip
Paros proxy
Browser Warnings
Attacking ApplicationLevel SSL Validation
The SSLTheft Payload
Hijacking Foundation HTTP Classes
The POSTTheft Payload
Analyzing Data
Driftnet
Building
Running
Exercises
Summary
Part Ⅱ. Securing
10. Implementing Encryption
Password Strength
Beware Random Password Generato
Introduction to Common Crypto
Stateless Operatio
Stateful Encryption
Master Key Encryption
GeoEncryption
GeoEncryption with Passphrase
Split ServerSide Keys
Securing Memory
Wiping Memory
Public Key Cryptography
Exercises
11. Counter Foreics
Secure File Wiping
DOD 5220.22M Wiping
ObjectiveC
Wiping SQLite Records
Keyboard Cache
Randomizing PIN Digits
Application Screehots
12. Securing the Runtime
Tamper Respoe
Wipe User Data
Disable Network Access
Report Home
Enable Logging
False Contacts and Kill Switches
Process Trace Checking
Blocking Debugge
Runtime Class Integrity Checks
Validating Address Space
Inline Functio
Complicating Disassembly
Optimization Flags
Stripping
They're Fun! They Roll! funrollloops
Exercises
13. Jailbreak Detection
Sandbox Integrity Check
Filesystem Tests
Existence of Jailbreak Files
Size of/etc/fstab
Evidence of Symbolic Linking
Page Execution Check
14. Next Steps
Thinking Like an Attacker
Other Revee Engineering Tools
Security Veus Code Management
A Flexible Approach to Security
Other Great Books
相關資源:
- [其他圖書]《經穴斷面解剖圖解·腹盆》(嚴振國)掃描版[PDF]
- [經濟管理]《激勵員工的18個大原則和180個小手段》掃描版
- [人文社科]《憲政的趨勢》[PDF]
- [其他圖書]《黑客對抗七十二變》[光盤鏡像]
- [計算機與網絡]《The Pragmatic Bookshelf開發叢書-Git實用指南》(Pragmatic Guide to Git)更新源代碼[PDF]
- [生活圖書]《圖解頸肩腰腿痛》掃描版[PDF]
- [文學圖書]《大衛·奧格威自傳》文字版[PDF]
- [文學圖書]《朱熹與中國文化》掃描版[PDF]
- [小說圖書]《七彩貓眼》掃描版[PDF]
- [少兒圖書]《趣味折紙游戲》掃描版[PDF]
- [英語學習資料]Alexandre Desplat -《獵殺本拉登》(Zero Dark Thirty)[FLAC] 資料下載
- [經濟管理]《經濟學的著名寓言:市場失靈的神話》(Famous Fables Economics)((美)丹尼爾·F·史普博)掃描版[PDF]
- [人文社科]《你在為誰讀書Ⅲ:讓自己無可替代》掃描版[
- [其他圖書]《獨特的公寓,2013最終版》(Unique Homes ,ultimate 2013)影印版[PDF]
- [電子雜志]《計算機應用文摘2015年》更新至10月上[PDF] 資料下載
- [教育科技]《給數學迷的500個挑戰性問題》清晰掃描版[PDF]
- [生活圖書]《中毒急救速查》掃描版[PDF]
- [人文社科]《信長之野望9岚世紀威力加強日文版》(Rlranseikipk)
- [人文社科]《山本五十六》(Isoroku Yamamoto)((日)加籐正秀)掃描版[PDF]
- [光盤游戲]《三國志11》(Romance of the Three Kingdoms XI)美版破解版[ISO]
- 《影像聖堂:Photoshop CS4圖層與通道技術精粹·彩圖版》掃描版[PDF]
- 《3D圖形卡15年發展史》[照片版][JPEG][RAR]
- 《UG NX 5中文版塑料模具設計實例精講》掃描版
- 《持續測試:使用Ruby, Rails, and JavaScript》(Continuous Testing: with Ruby, Rails, and JavaScript)英文文字版/更新EPUB版本/更新源代碼[PDF]
- 《Delphi 程序開發范例寶典(第2版)》(梁水)掃描
- 《CorelDRAW X4精華教程》掃描版[PDF]
- 《C++模板元編程》(C++ Template Metaprogramming)掃描版[PDF]
- 《Visual C# 2008大學教程(第三版)》(Visual C# 200
- 《C++編程思想(兩卷合訂本)》掃描版[PDF]
- 《現代電信手冊》(CRC Handbook of Modern Telecommunications, Second Edition)(Patricia A. Morreale & Kornel Terplan)文字版 第二版[PDF]
- 《用谷歌關鍵詞廣告賺大錢》掃描版[PDF]
- 《OReilly計算機圖書2013年4月合集》(OReilly Books Collection)英文文字版/EPUB/下載鏈接見資源介紹[PDF]
免責聲明:本網站內容收集於互聯網,本站不承擔任何由於內容的合法性及健康性所引起的爭議和法律責任。如果侵犯了你的權益,請通知我們,我們會及時刪除相關內容,謝謝合作! 聯系信箱:[email protected]
Copyright © 電驢下載基地 All Rights Reserved